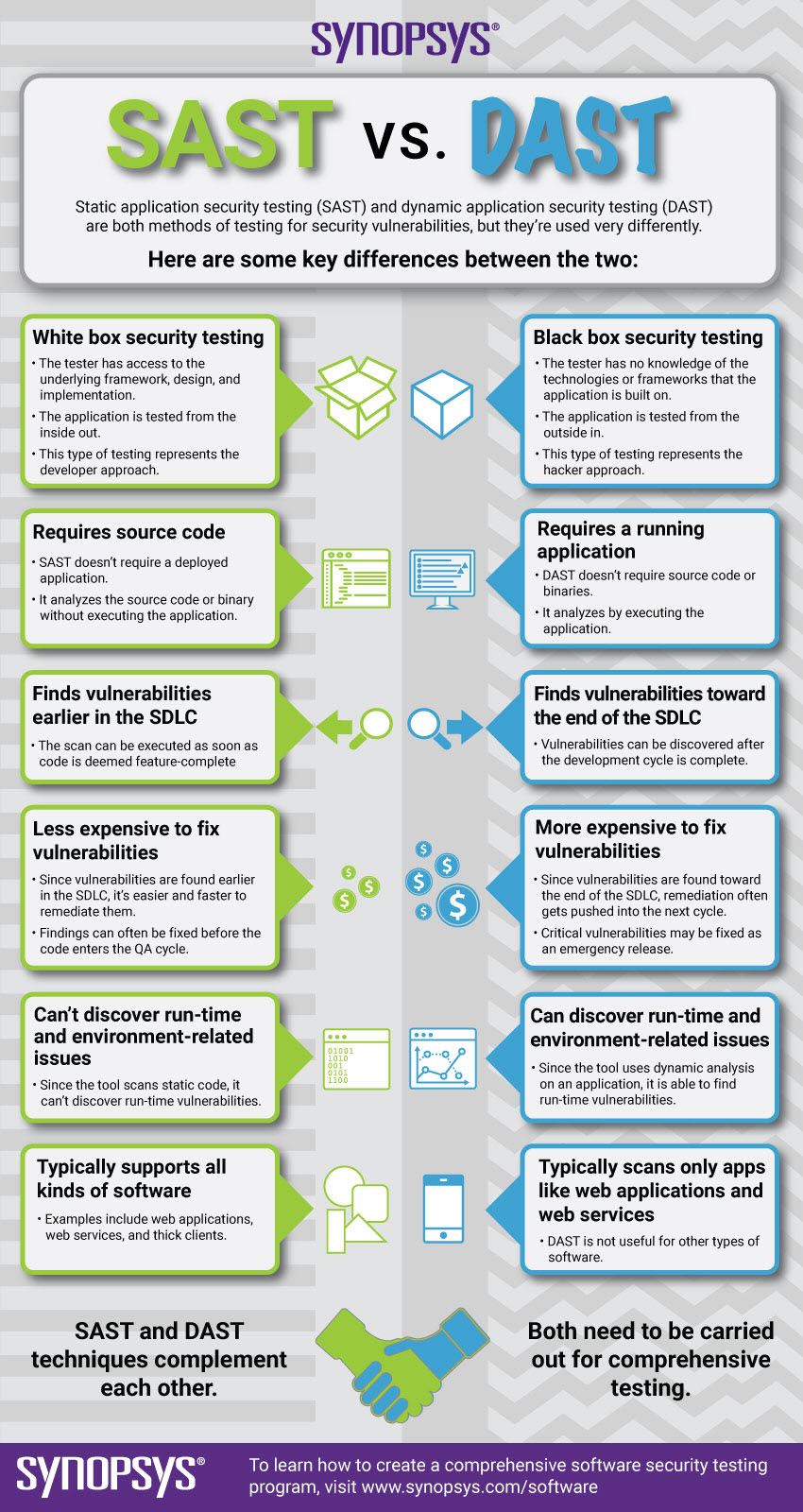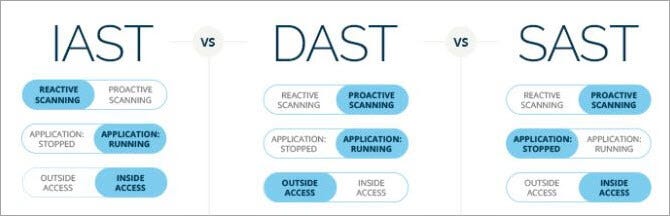
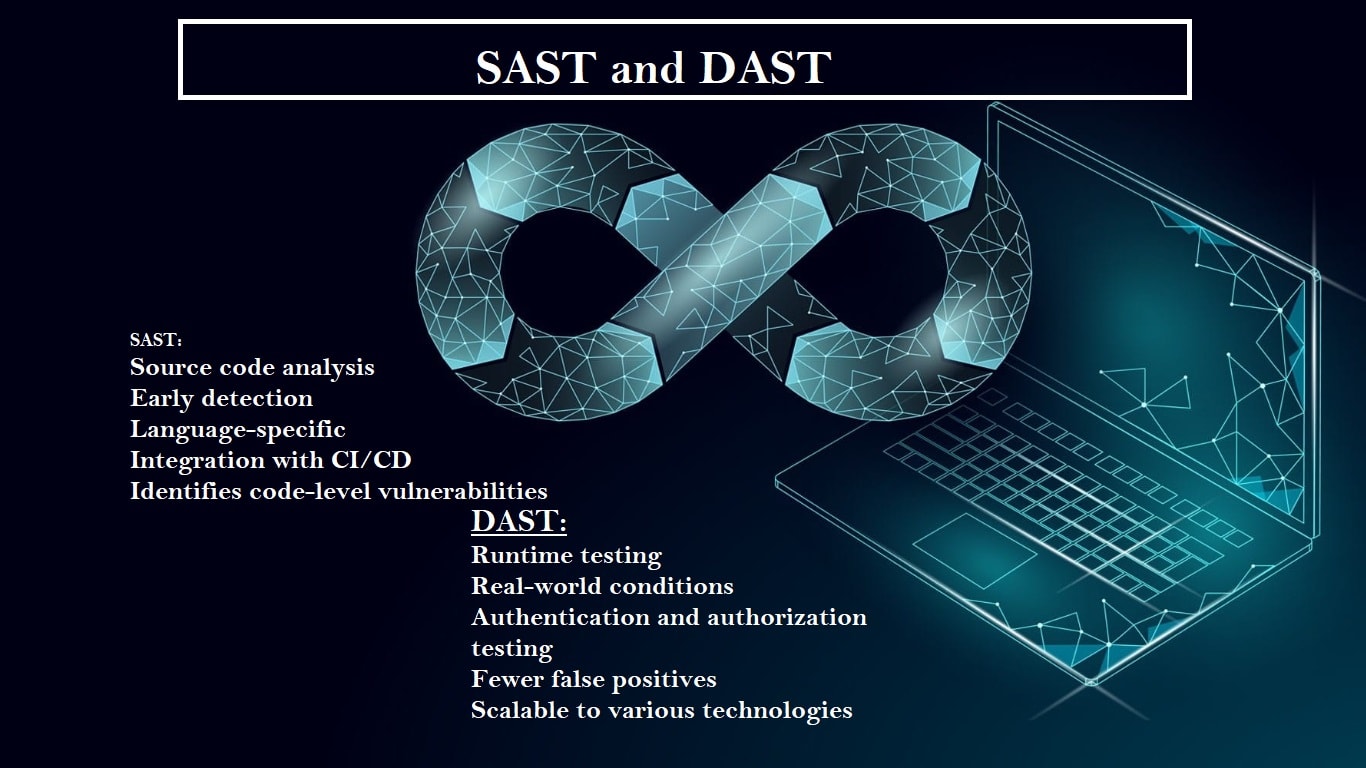
Ensuring Robust Application Security: Exploring SAST, DAST, and IAST for Comprehensive Protection | by Ranjan Singh | Medium

NST Cyber - Blogs - Can Continuous Threat Exposure Management (CTEM) Outperform DAST in Safeguarding Software Supply Chain Security?




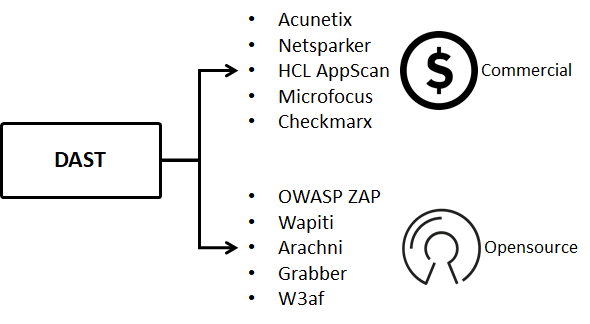
![10 Best Dynamic Application Security Testing Software [DAST Tools] 10 Best Dynamic Application Security Testing Software [DAST Tools]](https://www.softwaretestinghelp.com/wp-content/qa/uploads/2021/01/Acunetix.png)